Mirai is malware that infects devices such as cameras, Wi-Fi devices, and smart TVs.
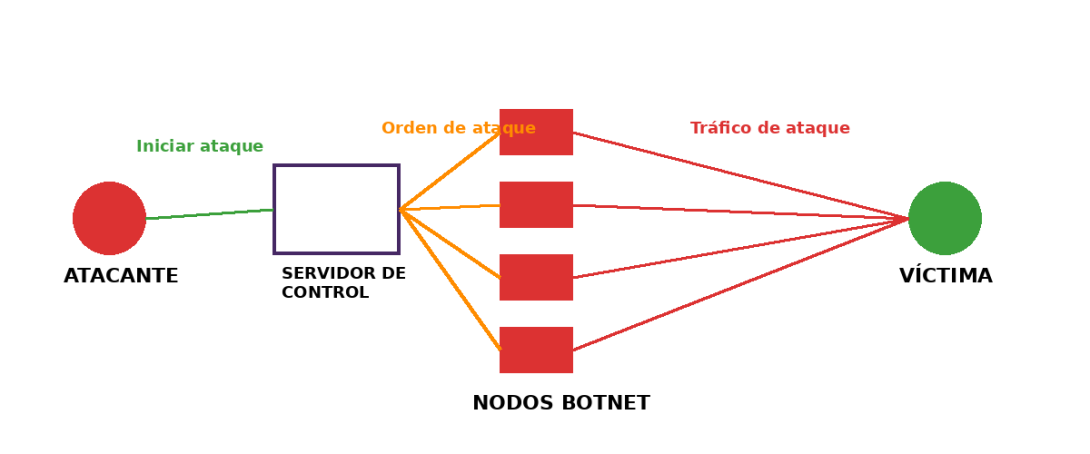
It turns these devices into a network controlled by attackers, known as a botnet.
This malware has been used to launch coordinated massive attacks. However, there are updates to its configuration.
The new variants have improved DDoS attacks. They are now larger, more distributed, and harder to block. Furthermore, the key innovation lies in the use of new malicious proxies.
• The attacker redirects traffic through them.
• They appear to be “normal users” from the outside.
This allows them to:
• Hide the attacker's identity.
• Evade blocks and security systems.
• Simulate legitimate traffic.
It's similar to using a VPN… but illegal and with hacked devices.
These innovations can be used primarily to preserve the attackers' anonymity and launch attacks on a larger scale.
Unlike just a few months ago, when this malware could take down a website, it can now maintain anonymity and perpetuate fraud.
They are becoming multifunctional platforms, not just attack tools. And this is extremely worrying:
• There are millions of vulnerable IoT devices
• Attacks are now:
o Harder to detect
o More profitable for attackers
o More persistent
Furthermore, the Mirai malware is already like a "base template" that others constantly reuse. Mirai has evolved from a DDoS tool to a complete cybercrime infrastructure.